blog.halosecurity.com/introducing-dark-web-monitoring
Preview meta tags from the blog.halosecurity.com website.
Linked Hostnames
8- 36 links towww.halosecurity.com
- 6 links toblog.halosecurity.com
- 3 links totwitter.com
- 2 links towww.linkedin.com
- 1 link toapp.halosecurity.com
- 1 link tosupport.halosecurity.com
- 1 link towww.facebook.com
- 1 link towww.youtube.com
Thumbnail
Search Engine Appearance
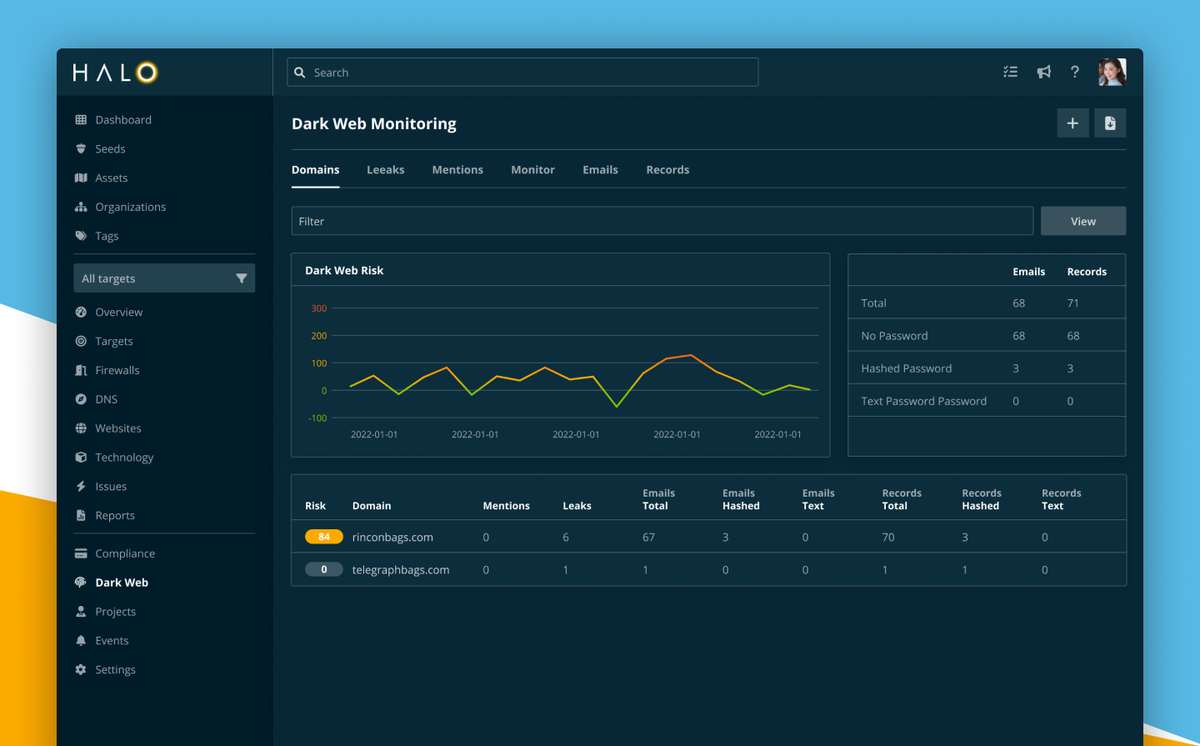
Introducing Dark Web Monitoring
In today's interconnected world, the dark web poses a significant threat to businesses like ours. Its anonymity and lack of regulation make it a prime breeding ground for cybercriminals to engage in illicit activities such as data breaches, stolen credentials, and the sale of sensitive information. That's why we're excited
Bing
Introducing Dark Web Monitoring
In today's interconnected world, the dark web poses a significant threat to businesses like ours. Its anonymity and lack of regulation make it a prime breeding ground for cybercriminals to engage in illicit activities such as data breaches, stolen credentials, and the sale of sensitive information. That's why we're excited
DuckDuckGo
Introducing Dark Web Monitoring
In today's interconnected world, the dark web poses a significant threat to businesses like ours. Its anonymity and lack of regulation make it a prime breeding ground for cybercriminals to engage in illicit activities such as data breaches, stolen credentials, and the sale of sensitive information. That's why we're excited
General Meta Tags
11- titleIntroducing Dark Web Monitoring
- charsetutf-8
- X-UA-CompatibleIE=edge
- HandheldFriendlyTrue
- viewportwidth=device-width, initial-scale=1.0
Open Graph Meta Tags
8- og:site_nameHalo Security Blog
- og:typearticle
- og:titleIntroducing Dark Web Monitoring
- og:descriptionIn today's interconnected world, the dark web poses a significant threat to businesses like ours. Its anonymity and lack of regulation make it a prime breeding ground for cybercriminals to engage in illicit activities such as data breaches, stolen credentials, and the sale of sensitive information. That's why we're excited
- og:urlhttps://blog.halosecurity.com/introducing-dark-web-monitoring/
Twitter Meta Tags
10- twitter:cardsummary_large_image
- twitter:titleIntroducing Dark Web Monitoring
- twitter:descriptionIn today's interconnected world, the dark web poses a significant threat to businesses like ours. Its anonymity and lack of regulation make it a prime breeding ground for cybercriminals to engage in illicit activities such as data breaches, stolen credentials, and the sale of sensitive information. That's why we're excited
- twitter:urlhttps://blog.halosecurity.com/introducing-dark-web-monitoring/
- twitter:imagehttps://blog.halosecurity.com/content/images/size/w1200/2024/03/dark-web-monitoring.png
Link Tags
11- alternatehttps://blog.halosecurity.com/rss/
- amphtmlhttps://blog.halosecurity.com/introducing-dark-web-monitoring/amp/
- canonicalhttps://blog.halosecurity.com/introducing-dark-web-monitoring/
- iconhttps://blog.halosecurity.com/content/images/size/w256h256/2022/06/icon-500.png
- stylesheethttps://blog.halosecurity.com/assets/built/screen.css?v=25e4c9e0d2
Links
51- https://app.halosecurity.com/user/security/darkweb/start?ref=blog.halosecurity.com
- https://blog.halosecurity.com
- https://blog.halosecurity.com/author/nick
- https://blog.halosecurity.com/critical-regresshion-vulnerability-exposes-millions-of-openssh-servers
- https://blog.halosecurity.com/easily-integrate-your-halo-security-findings-with-armorcode