www.roguelynn.com/words/explain-like-im-5-kerberos
Preview meta tags from the www.roguelynn.com website.
Linked Hostnames
17- 17 links towww.roguelynn.com
- 3 links toen.wikipedia.org
- 2 links towww.ietf.org
- 1 link tocontent.hccfl.edu
- 1 link todisqus.com
- 1 link tofortawesome.github.com
- 1 link tofreeipa.org
- 1 link toglyphicons.com
Thumbnail
Search Engine Appearance
Explain like I’m 5: Kerberos
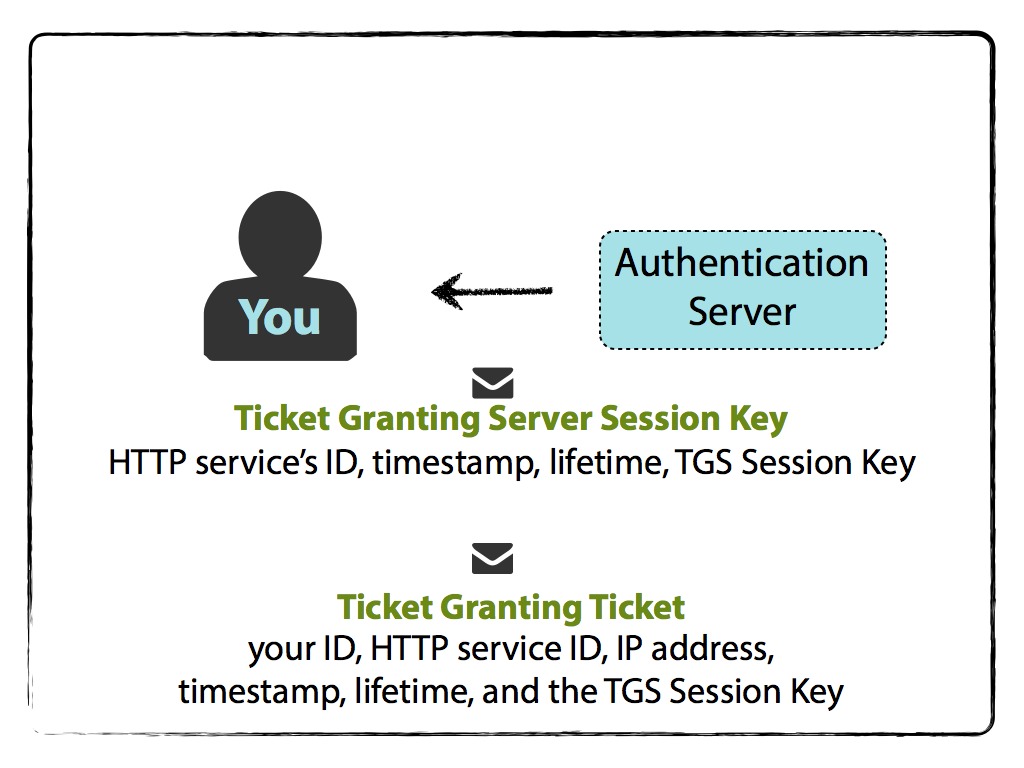
Explain like I’m 5 years old: Kerberos – what is Kerberos, and why should I care? While this topic probably can not be explained to a 5 year-old and be understood, this is my attempt at defragmenting documentation with some visual aids and digestible language. In a nutshell Basically, Kerberos comes down to just this: a protocol for authentication uses tickets to authenticate avoids storing passwords locally or sending them over the internet involves a trusted 3rd-party built on symmetric-key cryptography You have a ticket – your proof of identity encrypted with a secret key for the particular service requested – on your local machine (creation of a ticket is described below); so long as it’s valid, you can access the requested service that is within a Kerberos realm.
Bing
Explain like I’m 5: Kerberos
Explain like I’m 5 years old: Kerberos – what is Kerberos, and why should I care? While this topic probably can not be explained to a 5 year-old and be understood, this is my attempt at defragmenting documentation with some visual aids and digestible language. In a nutshell Basically, Kerberos comes down to just this: a protocol for authentication uses tickets to authenticate avoids storing passwords locally or sending them over the internet involves a trusted 3rd-party built on symmetric-key cryptography You have a ticket – your proof of identity encrypted with a secret key for the particular service requested – on your local machine (creation of a ticket is described below); so long as it’s valid, you can access the requested service that is within a Kerberos realm.
DuckDuckGo
Explain like I’m 5: Kerberos
Explain like I’m 5 years old: Kerberos – what is Kerberos, and why should I care? While this topic probably can not be explained to a 5 year-old and be understood, this is my attempt at defragmenting documentation with some visual aids and digestible language. In a nutshell Basically, Kerberos comes down to just this: a protocol for authentication uses tickets to authenticate avoids storing passwords locally or sending them over the internet involves a trusted 3rd-party built on symmetric-key cryptography You have a ticket – your proof of identity encrypted with a secret key for the particular service requested – on your local machine (creation of a ticket is described below); so long as it’s valid, you can access the requested service that is within a Kerberos realm.
General Meta Tags
17- titleExplain like I’m 5: Kerberos – roguelynn
- charsetutf-8
- X-UA-Compatiblechrome=1
- HandheldFriendlyTrue
- MobileOptimized320
Open Graph Meta Tags
4- og:titleExplain like I’m 5: Kerberos
- og:descriptionExplain like I’m 5 years old: Kerberos – what is Kerberos, and why should I care? While this topic probably can not be explained to a 5 year-old and be understood, this is my attempt at defragmenting documentation with some visual aids and digestible language. In a nutshell Basically, Kerberos comes down to just this: a protocol for authentication uses tickets to authenticate avoids storing passwords locally or sending them over the internet involves a trusted 3rd-party built on symmetric-key cryptography You have a ticket – your proof of identity encrypted with a secret key for the particular service requested – on your local machine (creation of a ticket is described below); so long as it’s valid, you can access the requested service that is within a Kerberos realm.
- og:typearticle
- og:urlhttps://www.roguelynn.com/words/explain-like-im-5-kerberos/
Twitter Meta Tags
5- twitter:cardsummary
- twitter:site@roguelynn
- twitter:creator@roguelynn
- twitter:titleExplain like I’m 5: Kerberos
- twitter:imagehttps://www.roguelynn.com/words/explain-like-im-5-kerberos/images/Kerb.004.jpg
Link Tags
10- canonicalhttps://www.roguelynn.com/words/explain-like-im-5-kerberos/
- shortcut icon/images/favicon.ico
- stylesheethttps://cdnjs.cloudflare.com/ajax/libs/highlight.js/9.11.0/styles/default.min.css
- stylesheet/css/reset.css?t=2024-05-17%2010%3a15%3a40.156512%20-0400%20EDT%20m%3d%2b0.263393876
- stylesheet/css/fonts.css?t=2024-05-17%2010%3a15%3a40.156512%20-0400%20EDT%20m%3d%2b0.263393876
Links
36- http://content.hccfl.edu/pollock/AUnixSec/MoronsGuideToKerberos.htm
- http://freeipa.org
- http://glyphicons.com
- http://k5wiki.kerberos.org/wiki/Pkinit_configuration
- http://l.ynn.me/Zxcew1